
When you want a proactive, vigilant approach to cybersecurity that aligns your corporate objectives with compliance, industry, and federal standards, turn to Pearl Solutions Group for cybersecurity services. We provide enterprise-level, industry-leading security, including dark web monitoring, password management, and other advanced security tools.
The Pearl team is ready to implement the individual cybersecurity services that will most effectively secure and protect your data:
What services can you expect when you entrust your cybersecurity to Pearl Solutions Group?
Here are the 15 ways we’ll protect your organization from a cyber-attack:







Would you like to learn more about cybersecurity services for your business?
Book a consultation with the Pearl Solutions cybersecurity team for more information.
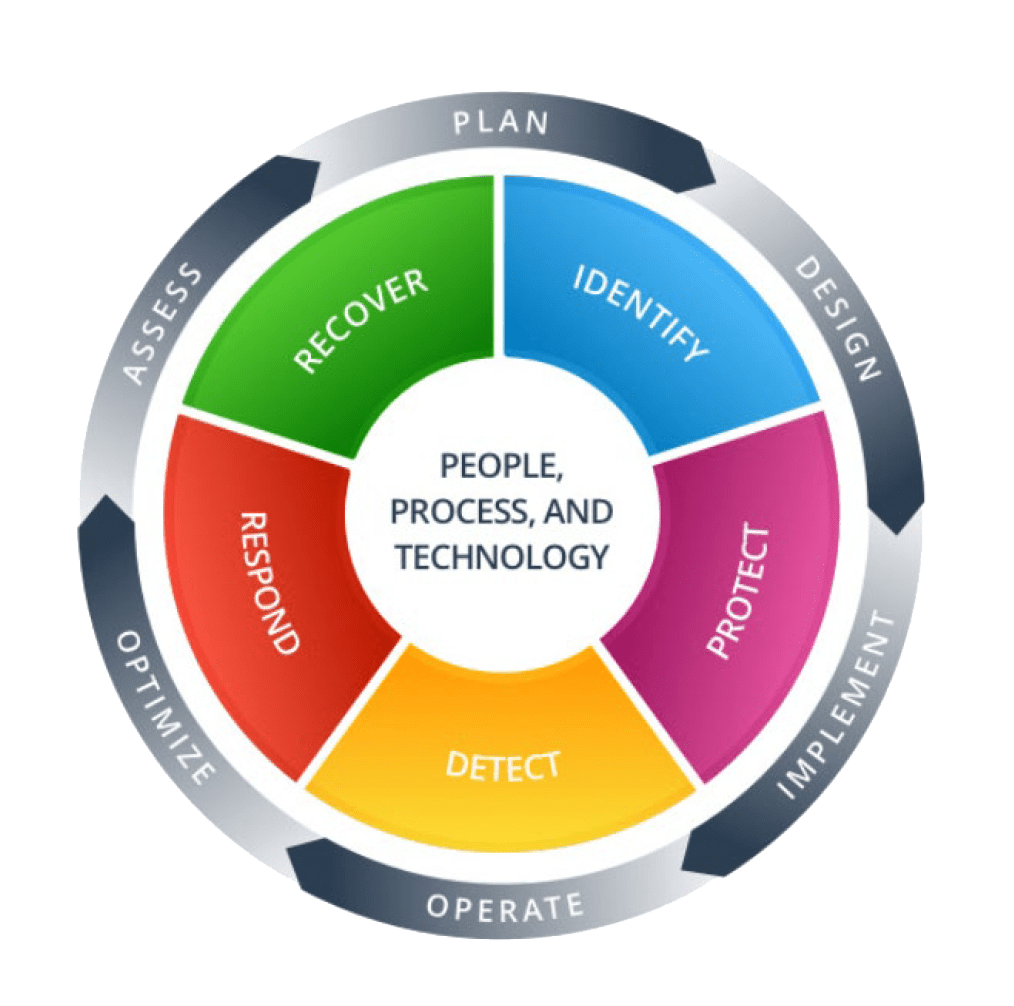
The cybersecurity team at Pearl Solutions Group works with our clients to educate, implement, and support a strong security posture. In addition to traditional measures like routine updates, tested backups, firewalls, and anti-virus, we provide the latest proactive solutions like dark web monitoring, advanced detection and response, and zero trust—all following NIST standards and keeping you compliant.
The best way to experience our team’s cybersecurity solutions expertise is to schedule a consultation. We’ll listen to your concerns, look for vulnerabilities, and suggest a cybersecurity package that protects what’s important.
We understand that cybersecurity can seem complex and expensive. We also know your employees need dependable, quick, and secure access to company data and their computers and devices. Our core values are about providing enterprise-grade services to businesses.
We’re really good at working with our customers’ budgets and providing best-practice solutions—because that’s what you deserve.
We follow the National Institute of Standards and Technology (NIST) framework and align your plan with corporate objectives that meet compliance standards and move you away from ad-hoc and reactive security efforts.
When you choose to work with Pearl Solutions, you won’t just get cybersecurity recommendations—you’ll gain a partner who’s dedicated to managing the cybersecurity measures that will keep your data secure.
Cybersecurity myths are often circulated as fact. Maybe you’ve heard a few of them:
We’ve worked very hard to find budget-friendly solutions, especially considering that the average breach costs a small business $53,970. Free services might offer some protection, but is it worth the risk?
Small businesses are the victims of most of today’s attacks because they are under-protected. We help secure your data, your customers, and your reputation from cybercriminals who see your small business’s vulnerabilities.
Most cyber-attacks are sophisticated enough to bypass a business’s basic security precautions. What worked yesterday will not be enough to protect against today’s threats. With custom cybersecurity solutions, you can be sure you’re getting the latest protection.
Are you ready to bypass the myths and protect your data with proven cutting-edge cybersecurity services? Pearl Solutions Group is here for you.
As a business, your greatest vulnerabilities probably lie in these areas:
As you think about the security of the data owned by you, your customers, and your employees, here are some things you can do to move forward with being cyber-secure:
We all know that IT is always changing. It’s important to establish a baseline and close existing vulnerabilities (and for this to happen on an ongoing basis). Cybersecurity should never be “set it and forget it.” If you can’t remember the date when you completed a risk assessment or if you’re relying on solutions from years past, now is an opportune time to determine the status of your cybersecurity ecosystem. We will help you!
Criminals are adept at creating emails that look and seem real to get you or someone on your team to wire money to a phony account. They might access your data and hold it ransom or they may impersonate a business you actually have a relationship with. The bad guys will go to great lengths to be sneaky and get you to send money—you may even have a conversation with them and not realize it!
Consider the chaos that will ensue after a breach. There’s possible social media coverage, lost customers, angry partners, and a damaged reputation. The impact creates a ripple effect, especially if you consider how security is actually a part of your customer experience. Also, customers will not be able to access their data because ransomware has locked your system.
It’s your customers’ data that needs to be protected—from ransomware, disgruntled employees, and more. Every business says they value their customers and want to provide good experiences. You can be the company that does it—starting with the protection of data.
Schedule a Consultation with Pearl Solutions
This step represents the most you can do for your customers and the protection of their data. There’s no substitute for complete cybersecurity professional services by experts you can trust. Book your consultation with Pearl Solutions today.
It’s a fact! We’re a premier cybersecurity services provider. But that’s just part of what we offer. Our clients also partner with us for these services:
We’re here to help you decide which services will do the most as you strive to reach your goals. Let’s discuss it today!
It can be hard to find a cybersecurity services company that remedies vulnerabilities professionally and is still personable and approachable. Our clients seem to think we do a pretty good job, though.
Wouldn’t you like to be able to say these things about your cybersecurity services provider?
You can, and it all starts when you book a consultation with Pearl Solutions Group.